A quick word about the Apple hack
(and how it affects you)
 Over the past couple of days, the tech news has been abuzz over the infection of select employee computers at Apple by OSX/Pintsized.A – a piece of malware programming that exploited a vulnerability in the Java web plug-in.
Over the past couple of days, the tech news has been abuzz over the infection of select employee computers at Apple by OSX/Pintsized.A – a piece of malware programming that exploited a vulnerability in the Java web plug-in.
The code plants a backdoor on compromised computers, bypassing your computer’s firewall by pretending to be a printing operation. This could allow cybercriminals to run commands remotely on your computer – for whatever nefarious goals they have in mind. Check out this Intego blog post for details.
Both Apple (Java 6) and Oracle (Java 7) have quickly issued updates to plug the hole. Their respective auto-updaters should handle this for you. (Use Apple’s Software Update and/or open the System Pref for Java.)
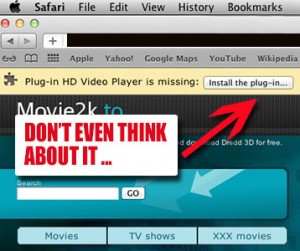
No more Apple plug-in
In addition to the fix, the Apple update completely removes the Apple Java 6 web browser plug-in as well as the Java Preferences application since is no longer required to configure applet settings. So from this point forward, Java 6 on the Mac is restricted to desktop Java applications only. From now on, plug-in duties will be handled via the official Java 7 release from Oracle.
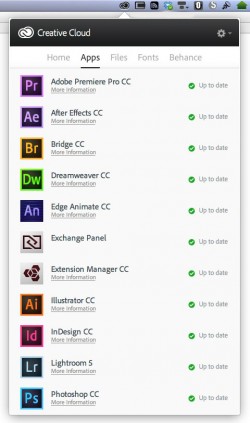
 Even so, it’s a good idea to disable the plug-in in your browser and turn it on only for the times you need it. Examples if this include web-based GoToMeeting sessions .. or if you have a Box.net cloud storage account. Open the Java 7 System Pref (which will then open a separate application), go to the Security Tab, and uncheck the “Enable Java content in the browser” box.
Even so, it’s a good idea to disable the plug-in in your browser and turn it on only for the times you need it. Examples if this include web-based GoToMeeting sessions .. or if you have a Box.net cloud storage account. Open the Java 7 System Pref (which will then open a separate application), go to the Security Tab, and uncheck the “Enable Java content in the browser” box.
For those who think they may have been compromised with this exploit (you would have had to be in some pretty specific places – most notably an iPhone developer forum – that’s where programmers for Apple, Facebook, and Twitter got it), Apple should be releasing a malware detection tool soon.